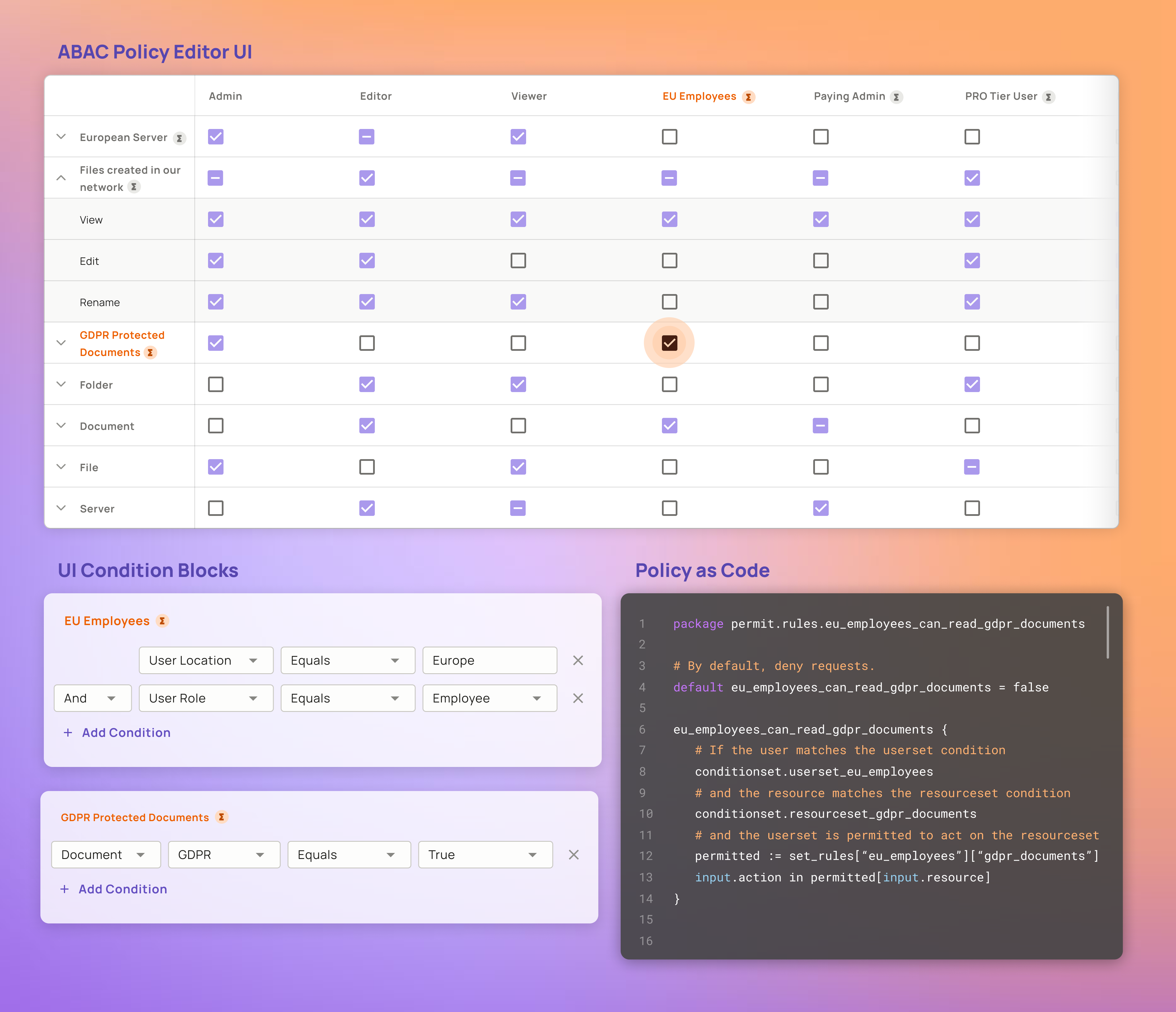
Limiting the visibility of sensitive data items through attribute-based access control (ABAC) - PegaWiki
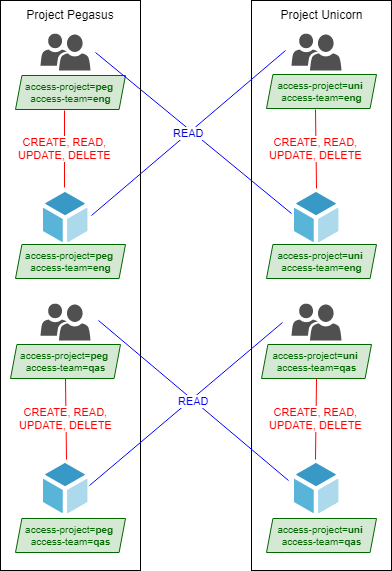
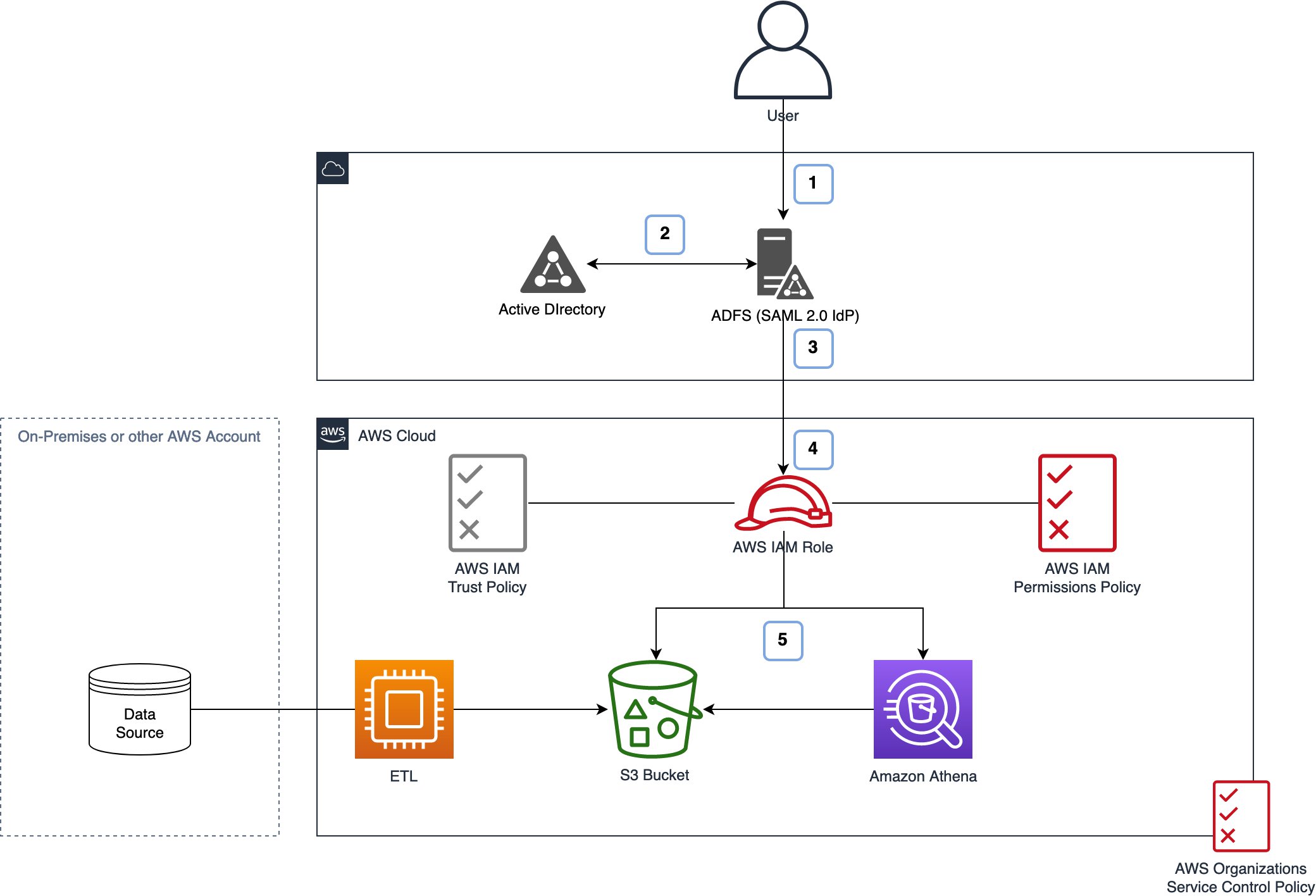
IAM tutorial: Define permissions to access AWS resources based on tags - AWS Identity and Access Management

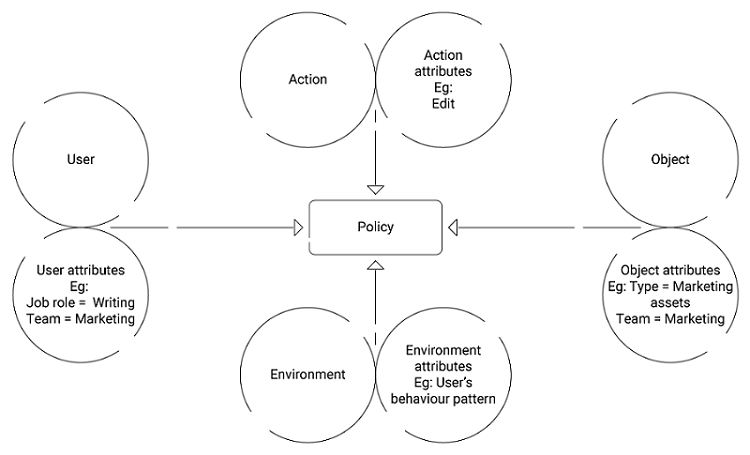
Five Cornerstones of ABAC: Policy, Subject, Object, Operation Type and... | Download Scientific Diagram